When you hear the term Access Control you would be forgiven for not instantly knowing what it was, but we actually encounter these systems in our everyday lives more than you might think.
Access Control systems are instilled in all facets of our lives, from the fingerprint scanner on your phone, to the key fob you use to get into your gym or apartment.
The basic concept of Access Control is a system that either grants or denies entry to a lock or door by determining the identity of the person; this can be done by biometrics, passwords, key cards, and everything in between.
In this crash course, we will be taking a look at Access Control, how it works, the three core types, and some pros & cons of implementing Access Control in your business.
- Access Control 101
- Access Control Types
- Pros of Access Control
- Potential Challenges of Access Control
How does Access Control Work?
Access Control is an umbrella term for a lot of different security systems that are encompassed by the core idea of granting or denying access.
To simplify, Access Control systems allow users to unlock a door by determining their identity. If you are someone who has permission to be granted access the lock will open, and if you are not, you will be denied entry.
Access Control has a few core elements across the majority of systems, let us take a look at some of these aspects.
- Credential - this is what the user presents to be granted access, this can be either token-based (a key card or fingerprint) or knowledge-based (a password or pin).
- User - the person permitted to access the entry point or lock.
- Reader - the part of the system that scans a user’s credential to determine access or deny entry.
- Controller - where the information scanned by the reader is sent, which will decide whether or not they have permission to access the door.
- Access Point - the place the user is trying to get into, this can be a lock, door, or even encrypted files.
Now let us put these terms together to see how Access Control works…The User presents their Credential to the Reader and the Controller determines if they are eligible to enter the Access Point. This all happens in a matter of seconds.
To contextualise here is how an Access Control system works in practice.
You have control of your system, who comes in, who goes out, where they can access, and even granting temporary permission. We find these Access Control devices everywhere, in all industries from airports, to health clubs and gyms, to offices, to car parks.
What are the 3 Types of Access Control?
Access Control can be broken down into a few different areas, and there is a whole range of unique systems. With this being said, however, there are three different permission levels you can choose which help you manage access.
Role-Based Access Control (RBAC)
As the name implies, access is granted to people who have the same job or role. This means the system will grant access to users based on their level of privilege. Users can only access areas that are determined by their job.
So, for instance, everyone in security would have full access to perform their job successfully, whereas the front of house staff members would only have access to areas in their department.
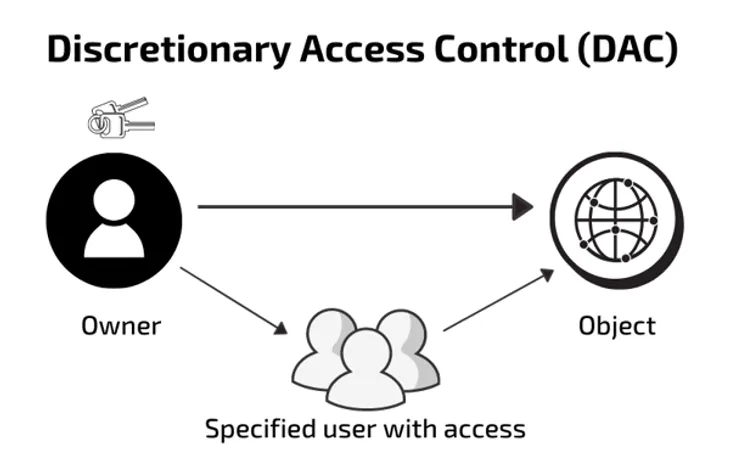
Discretionary Access Control (DAC)
DAC allows for control over each access or entry point. This means that each separate door or reader has a different list of authorised users which is set by the owner.
Discretionary Access Control allows for a more customisable option. Especially if you want to control who access levels more than RBAC. This works well in organisations that have siloed information or lots of different departments and users.
Mandatory Access Control (MAC)
Out of the three types, MAC is the most controlled and restricts access to a higher extent. Rules can typically be set for this type of Access Control which keeps users limited and security increased.
Using this method is good because it can be controlled from a centralised location, such as a security office and can standardise your security policies across all of your access points. MAC is commonly used in high-security environments such as warehouses, hospitals, and schools.
Benefits of Access Control
Access Control systems each have their own unique benefits and uses which will appeal to different industries, businesses, and security levels.
In this section, we will take a look at the broad benefits of setting up an Access Control system within your business. If you are interested in more specific areas of Access Control you can research their benefits in more depth, from marinas to gyms to hotels.
Security Benefits of Access Control
Limit External Access - having an Access Control system you can reduce the likelihood of an external breach, and in the event of one, you will know where they are and when.
Reduce Internal Threats - with Access Control you will be able to grant access to different staff in various areas. This means you can ensure users only have access to what they need. If only a few people can get to a certain area, they are less likely to pose a security risk.
Control Access Times - depending on your system, you can limit when users have access. For example, if someone is not on shift, you can deny access and vice versa. Keeping you in control and security tight.
Operational Benefits of Access Control
Reduced Costs - implementing Access Control will allow your business to limit the need for 24/7 security. You will not need to hire around the clock security teams. You can also verify identification without a manual check, this has been utilised in airports and borders. To learn more about what to budget for, see our guide on access control system costs.
Save Resources - almost everyone can say they have at some point lost or misplaced their keys, it happens to the best of us. With an Access Control system, you will save time, money, and resources by updating from lock and key methods.
Plays Well With Others - regardless of your current security system, Access Control as a whole can be integrated and combined with relative ease. As most of the Access Control options are designed to be part of a wider security strategy. For example, integrating biometric access control with existing systems is increasingly common.
General Benefits of Access Control
Safer Work Environment - not only can you limit who can come in or out, but you can ensure your building is safe to exit in the event of an emergency. For instance, in a power cut or fire, all the doors can be unlocked so staff can safely navigate around the building. Features like anti-passback also help manage the flow of people entering and exiting your premises.
One Credential to Rule Them All - you can programme your Access Control system to grant users access to multiple doors and locations. This means you could hypothetically use one Key Fob as opposed to multiple sets of keys.
Visitor Permissions - if you are a business that needs to grant temporary access or has a lot of visitors coming in and out, Access Control can offer a viable solution. Most systems give easy ways to grant visitors permission or give temporary access.
3 Challenges of Access Control
No system is without flaws or challenges. Regardless of your business type or security infrastructure they can present themselves. However, some overarching issues can arise when you are trying to implement an Access Control system.
Let us look at three of the most common challenges you might come across.
Reluctance to Change
As with any major operational change you are likely to come across people who are reluctant to change and are opposed to updating systems.
A phrase you hear a lot in the security industry is “if it ain’t broke, don’t fix it”, unfortunately, this is a risky strategy and an outdated opinion.
To put this into context, let us say your business uses lock and key. You are not only compromising your security and inviting criminal activity, but you are creating operational issues with the potential of lost time, keys, and resources.
The rise of Access Control and the decline of lock and key is certainly no coincidence. As we have already looked at, there are a whole variety of benefits to implementing an Access Control system in your business.
Adoption and Training Time
A common challenge that businesses encounter when looking into Access Control is not wanting to spend the time and effort training their staff.
Depending on the system you choose, training can be a very simple process. For the majority of users, it will be as easy as scanning a barcode, tapping a fob, or using a fingerprint.
The administrator will be the main user who needs more training as they will be the one who is in charge of the system. But, with most types of Access Control learning how to use the systems is pretty rudimentary.
Choosing the Right System
As we have alluded to in this guide, there are a lot of different systems that come under Access Control, and knowing which one will be best suited to your business is incredibly important.
Businesses often struggle to decide which one will be the best fit and often will resort to doing nothing and sticking with their traditional system.
It does not have to be an uphill battle, however, finding the right solution for your business can be easier than you think. Our guide on how to install access control walks you through the process step by step.
Although they are certainly different systems suited to business types the choice is entirely yours. Factors like budget, amount of users, and current security systems could help you determine which will work for you.
Summary of Access Control
Access control and it’s uses can span across a whole range of industries and use cases. From the more straightforward physical access control to complex systems using access control software.
Security requirements are changing constantly, coupled with the growth of technologies such as IoT and RFID tags and we have an industry where new physical access control solutions are always emerging.
This can be a blessing and a curse for anyone looking to install access control as the options can be endless.
It’s important to consider your business objectives when selecting an access control system. It’s also important to ask:
- Is it compatible with 3rd party integrations and hardware?
- Is it easy and safe to install and configure?
- Is technical support offered as part of the system?
- Does it support multiple types of credentials such as QR codes, mobile credentials, cards, fobs and biometrics?
- Does it use an industry-standard protocol like Wiegand?
- Does it integrate with our time management and counting systems?
- Does it offer OEM integration for flexibility and future-proofing?
If you’re interested in learning more about the different types of access control available, visit the Nortech blog to learn more.